What Is Push-Bombing & How Can You Prevent It?
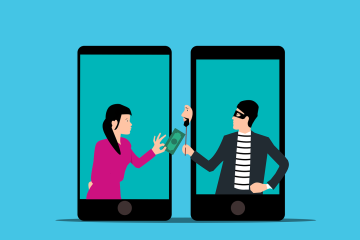
Cloud account takeover has become a major problem for organizations. Think about how much work your company does that requires a username and password. Employees end up having to log into many different systems or cloud apps. Hackers use various methods to get those login credentials. The goal is to Read more…